One command. 25 testers.
Zero cost.
breakit launches AI personas with real browsers against your web app.
A form abuser. A confused grandma. A skeptical buyer. An angry subscriber.
They find bugs, UX friction, and trust issues — then write them up with screenshots, priority scores, and fix suggestions.
npx breakit test https://your-app.comPaste a public URL, get a report in ~5 minutes. No account needed.
Meet your testers
Confused Grandma
Gets lostMisreads labels, clicks wrong things, gets lost.
Angry Subscriber
Tries to cancelTries to cancel, looking for dark patterns.
Form Abuser
Breaks inputsXSS, SQL injection, 10k-char strings, empty submits.
Skeptical Buyer
Doubts claimsChecks pricing, proof, trust signals.
Impatient Teenager
Zero patienceDouble-clicks everything, rage-clicks spinners.
Screen Reader User
Keyboard onlyARIA, headings, keyboard-only.
Privacy Hawk
Fights trackingCookie consent, trackers, privacy messaging.
Speed Runner
Shortest pathMain task in minimum clicks, zero tolerance for bloat.
Enterprise Evaluator
Checks complianceSSO, compliance, team features.
Non-Native Speaker
Reads literallyVague labels, idioms, unclear instructions.
...and 15 more. npx breakit test --pack all
Not a wall of AI text. A report you can actually work from.
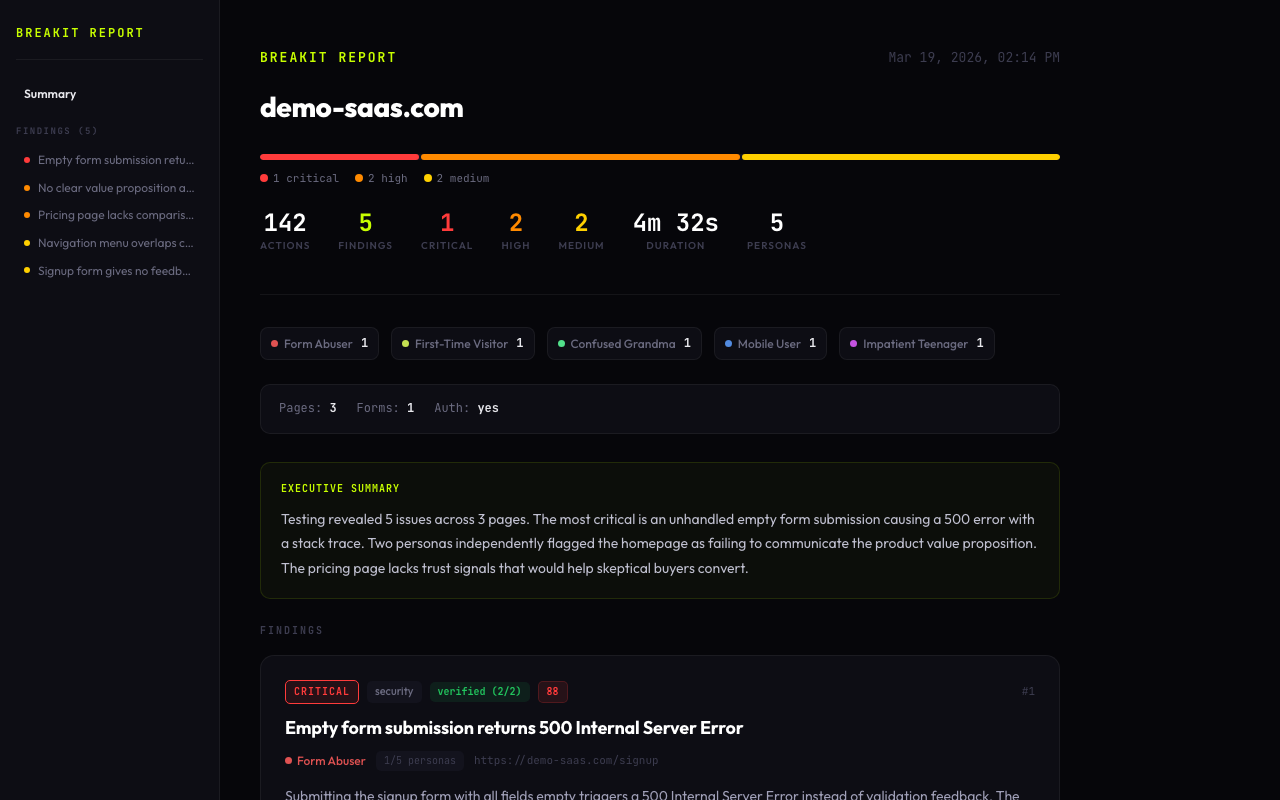
breakit groups duplicate findings, scores them by priority, and shows what happened with screenshots and reproduction steps. You can skim the summary, jump into individual issues, or compare runs after fixes.
Good enough for a solo launch check. Structured enough to drop into a team workflow.
Paste your URL
Point breakit at any public site or preview deployment.
Personas explore your site with real browsers
Each persona clicks, types, navigates, and tries to complete tasks from a different angle.
One report — everything scored and prioritized
Findings are deduplicated, scored 0-100, and packaged with screenshots and repro steps.
Personas explore independently, share findings to avoid duplicates, and produce a single scored report.
Browser mode: full interactive sessions | Snapshot mode: page screenshots + structure analysis, faster
Why Not Just Ask ChatGPT?
Because “this looks fine” is not a test result.
| Capability | breakit | Asking ChatGPT | Manual testing | Lighthouse / axe |
|---|---|---|---|---|
| Uses a real browser | Yes | No | Yes | Partial |
| Clicks through flows | Yes | No | Yes | No |
| Fills forms and hits edge cases | Yes | No | Yes | No |
| Multiple perspectives | 25 personas | Usually 1 | A few, if you have time | No |
| Screenshots and repro steps | Yes | Rarely | Sometimes | No |
| Re-runnable after fixes | Yes | Not really | Expensive | Yes |
| Works in CI | Yes | No | No | Yes |
| Cost to try | Free | Paid chat time | Expensive | Free |
Yes
No
Yes
Partial
Yes
No
Yes
No
Yes
No
Yes
No
25 personas
Usually 1
A few, if you have time
No
Yes
Rarely
Sometimes
No
Yes
Not really
Expensive
Yes
Yes
No
No
Yes
Free
Paid chat time
Expensive
Free
Lighthouse checks technical quality. breakit checks whether the experience makes sense to different kinds of people. You probably want both.
Use It Before Deploys, Not Just Before Launch
breakit can run in GitHub Actions, emit SARIF, and fail the build when findings cross your severity threshold.
Your test suite tells you whether the flow still works. breakit helps tell you whether the flow still makes sense.
Run in CI
Use the GitHub Action and test every deploy.
- uses: petrkindlmann/breakit@v1
with:
url: ${{ env.DEPLOY_URL }}
api-key: ${{ secrets.GEMINI_API_KEY }}Fail on serious findings
Set a severity threshold and block risky releases.
npx breakit test https://staging.app.com \
--severity-threshold highBrowser mode
Full Playwright runs for forms, flows, uploads, and JS-heavy pages.
npx breakit test https://app.com \
--pack qaSnapshot mode
Faster, cheaper checks when you just want broad coverage.
npx breakit test https://app.com \
--mode snapshot --pack uxCompare fixes
Run it again and see what improved, what regressed, and what still hurts.
npx breakit test https://app.com \
--compare ./previous-raw.jsonOpen source, local-first
No platform account. No hosted dashboard required.
export GEMINI_API_KEY=...
npx breakit test https://your-app.comSee A Run From Start To Finish
Watch breakit launch personas, explore a site, and produce a report with ranked findings.
$ breakit run https://demo-app.comClicked "Deploy to Production" thinking it sends an email
Injected <script>alert(1)</script> in bio field — it rendered!
Navigation menu overlaps content at 390px viewport
Double-clicked "Submit" — form submitted twice, duplicate entry
Could not find pricing page from homepage — no nav link
Pasted 50,000 chars into "Name" field — page froze for 4s
Typed phone number in email field, got cryptic "ERR_VALIDATION"
Hit back button during checkout — cart emptied, no recovery
Tap target for "Delete Account" is only 24x24px
Signup flow has 7 required fields with no progress indicator
Empty form submission returns 500 Internal Server Error
Clicked logo expecting to go home — nothing happened
Rage-clicked loading spinner 12 times — spawned 12 API calls
Horizontal scroll on /settings — content overflows viewport
"Get Started" redirected to login with no signup option visible
SQL injection in search: ' OR 1=1-- returned all users
Clicked "Deploy to Production" thinking it sends an email
Injected <script>alert(1)</script> in bio field — it rendered!
Navigation menu overlaps content at 390px viewport
Double-clicked "Submit" — form submitted twice, duplicate entry
Could not find pricing page from homepage — no nav link
Pasted 50,000 chars into "Name" field — page froze for 4s
Typed phone number in email field, got cryptic "ERR_VALIDATION"
Hit back button during checkout — cart emptied, no recovery
Tap target for "Delete Account" is only 24x24px
Signup flow has 7 required fields with no progress indicator
Empty form submission returns 500 Internal Server Error
Clicked logo expecting to go home — nothing happened
Rage-clicked loading spinner 12 times — spawned 12 API calls
Horizontal scroll on /settings — content overflows viewport
"Get Started" redirected to login with no signup option visible
SQL injection in search: ' OR 1=1-- returned all users
Try it on your own site
npx breakit test https://your-app.comPublic URL in, report out. About 5 minutes.